Wazuh
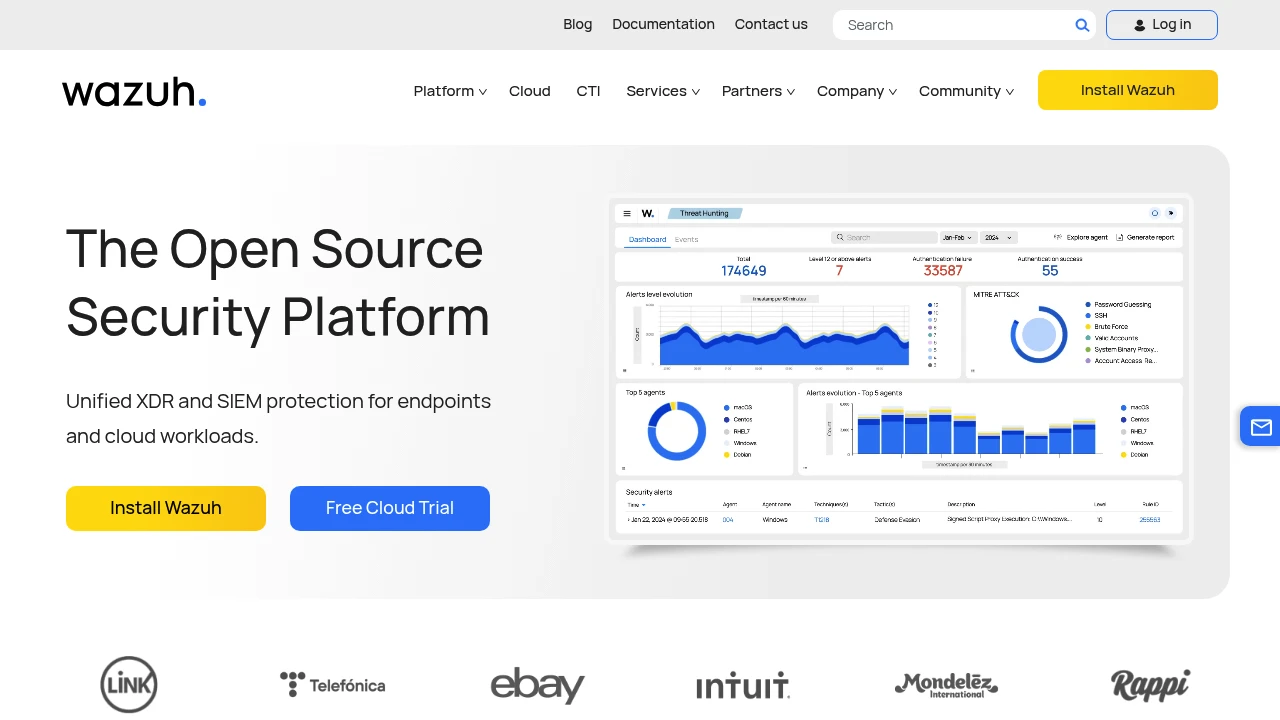
Wazuh is a free, open-source security platform that unifies XDR and SIEM capabilities for endpoint protection, threat detection, and compliance monitoring across IT and OT environments.
Most OT environments have zero security visibility. PLCs, SCADA systems, and HMIs were designed for reliability, not security — they run on flat networks with no logging, no intrusion detection, and no compliance monitoring. When IEC 62443 or NIST 800-82 auditors come knocking, the answer is usually a spreadsheet.
Wazuh fills this gap without a six-figure license. It's the most widely deployed open-source security platform (15K+ GitHub stars, 474 contributors, active since 2015), and it works across both IT endpoints and OT gateway systems. Plant engineers use it alongside dedicated OT-specific tools like Suricata for network IDS.
What it does
Platform components
- Wazuh Indexer — Stores and indexes security events (fork of OpenSearch)
- Wazuh Server — Analyzes data from agents, runs detection rules, triggers alerts
- Wazuh Dashboard — Web UI for searching, visualizing, and investigating security events
- Wazuh Agent — Lightweight agent deployed on endpoints (Linux, Windows, macOS, containers)
Core capabilities
- File Integrity Monitoring (FIM) — Track changes to SCADA config files, PLC project files, HMI configurations. Critical for detecting unauthorized modifications.
- Vulnerability Detection — Correlates software inventory with CVE databases. Flags known-vulnerable packages on OT gateways and historians.
- Log Analysis & Correlation — Ingests syslog, Windows events, application logs. 3000+ built-in detection rules.
- Compliance Monitoring — Built-in rulesets for PCI DSS, GDPR, HIPAA, NIST 800-53, CIS benchmarks. Configuration assessment scans against security baselines.
- Active Response — Automated countermeasures: block IPs, disable accounts, run custom scripts on detection.
OT-specific use cases
- Monitor Rapid SCADA and other SCADA platforms for unauthorized file changes
- Detect configuration drift on OT gateway servers
- Track user authentication on historian and MES servers
- Feed alerts to TheHive for security orchestration and automated response playbooks
Deployment
| Method | Use case | Min resources |
|---|---|---|
| Docker Compose | Quick evaluation, small deployments | 4 CPU, 8GB RAM |
| Kubernetes (Helm) | Production, multi-site scaling | Cluster with 3+ nodes |
| Single server | All-in-one for small sites | 4 CPU, 8GB RAM, 50GB disk |
| Wazuh Cloud (SaaS) | Managed service, no infrastructure | Starts at $500/mo |
| AWS Marketplace AMI | One-click AWS deployment | m5.xlarge or larger |
Pricing
The platform itself is free (GPLv2). Real costs:
- Self-hosted: $0 licensing. Budget for hardware ($200-500/mo for a 100-agent deployment) and ops time to tune rules and manage alerts.
- Professional support: ~$1,000/year from Wazuh Inc.
- Wazuh Cloud: From $500/month for managed SaaS.
- Log storage: Can be significant at scale — $20-30K/year for enterprise volumes. Use retention policies aggressively.
Limitations
- Not OT-native — Wazuh monitors endpoints and logs, not industrial protocols. It won't parse Modbus or S7 traffic. Pair it with Suricata or Zeek for network-level OT IDS.
- Resource-hungry at scale — The OpenSearch-based indexer needs serious RAM. A 500-agent deployment wants 16-32GB RAM minimum for the server stack.
- Alert fatigue — 3000+ built-in rules generate noise out of the box. Expect 2-4 weeks of tuning before the alert stream is useful.
- GPLv2 license — Not permissive. If you modify and distribute the source, you must release changes. For most manufacturing users (running, not distributing), this doesn't matter.
- No built-in AI/ML — Detection is rule-based. For anomaly detection, you need to feed Wazuh data into a separate ML pipeline or use Elastic ML on top.